The Middle East has always had a mixed history when it comes to cybersecurity measures. While countries like Israel, the UAE, and Saudi Arabia have been on par with global powers in terms of their security strategies, Jordan, Yemen, and Oman have extremely weak cybersecurity measures due to political instability, limited resources, and a lack of awareness. In general, however, the Middle East is undergoing a phenomenal digital transformation. The commercial success of locations like Dubai, Abu Dhabi, and Saudi Arabia has transformed them into epicenters for potential cybercrime.[1]
Earlier this month, a team of cybersecurity researchers uncovered a new iteration of a malware framework called EAGERBEE which has specifically targeted Internet Service Providers and government bodies in the Middle East. The latest version of EAGERBEE (aka Thumtais) has more sophisticated backdoor features, such as a service injector which allows itself to deploy as a hidden backdoor on a system. Additionally, it features plugins that enable payload delivery, file access, and remote-control functionalities. The evolution of this malware has been touted as a notable advancement in malware injection, making it more potent and dangerous than its earlier versions.[2]

[Image Source: https://www.techzim.co.zw/2022/07/kaspersky-finds-cybersecurity-backdoor-targetting-african-govts-ngos/]
Understanding EAGERBEE and its Detection:
EAGERBEE is a type of malware specifically designed to target web browsers and their extensions. Its primary goal is to steal sensitive information, such as login credentials, financial data, and other personal details, from infected systems. Unlike some malware that relies on obvious signs of infection, EAGERBEE operates stealthily, often going unnoticed until significant damage has been done.
This malware was initially identified by Elastic Security Labs, and linked it to a state-sponsored cyber-espionage group known as REF5961. It was observed in cyber-espionage attacks against Southeast Asian government agencies and linked to the Chinese nation-backed hacking collective, which Sophos, a British security firm tracked as “Crimson Palace.” EAGERBEE was also deployed in multiple organizations in East Asia, with two of them compromised through the nefarious ProxyLogon vulnerability (CVE-2021-26855) in Exchange servers. After the breach, malicious webshells were uploaded and used to execute commands on the affected servers.[3]
Modus Operandi of REF5961 Infiltration:
The REF5961 hacking group employs a series of sophisticated steps to breach and exploit target systems:
- Entry Point: They often begin by exploiting known vulnerabilities in widely used software. For instance, they have taken advantage of the ProxyLogon flaw in Microsoft Exchange servers (CVE-2021-26855) to gain unauthorized entry.[2]
- Stealth Mode: Once inside, they deploy malware like the EAGERBEE backdoor. This malicious software allows them to maintain long-term access, execute commands, and manage files on the compromised systems without raising any suspicion.[2]
- Access Elevation: To deepen their control, REF5961 seeks higher-level permissions and moves laterally across the network. They utilize tools such as the BLOODALCHEMY backdoor, which is injected into legitimate processes to avoid detection.[4]
- Data Exfiltration: With control established, they gather and transmit sensitive information from the target’s environment back to their servers, focusing on data that aligns with their espionage objectives.
Throughout these stages, REF5961 employs advanced techniques to remain undetected, including:
- DLL Sideloading: They misuse legitimate applications to load malicious DLLs, helping them blend in with normal system operations.[4]
- Obfuscation: By encrypting or disguising their code, they make it challenging for security tools to identify their malicious activities
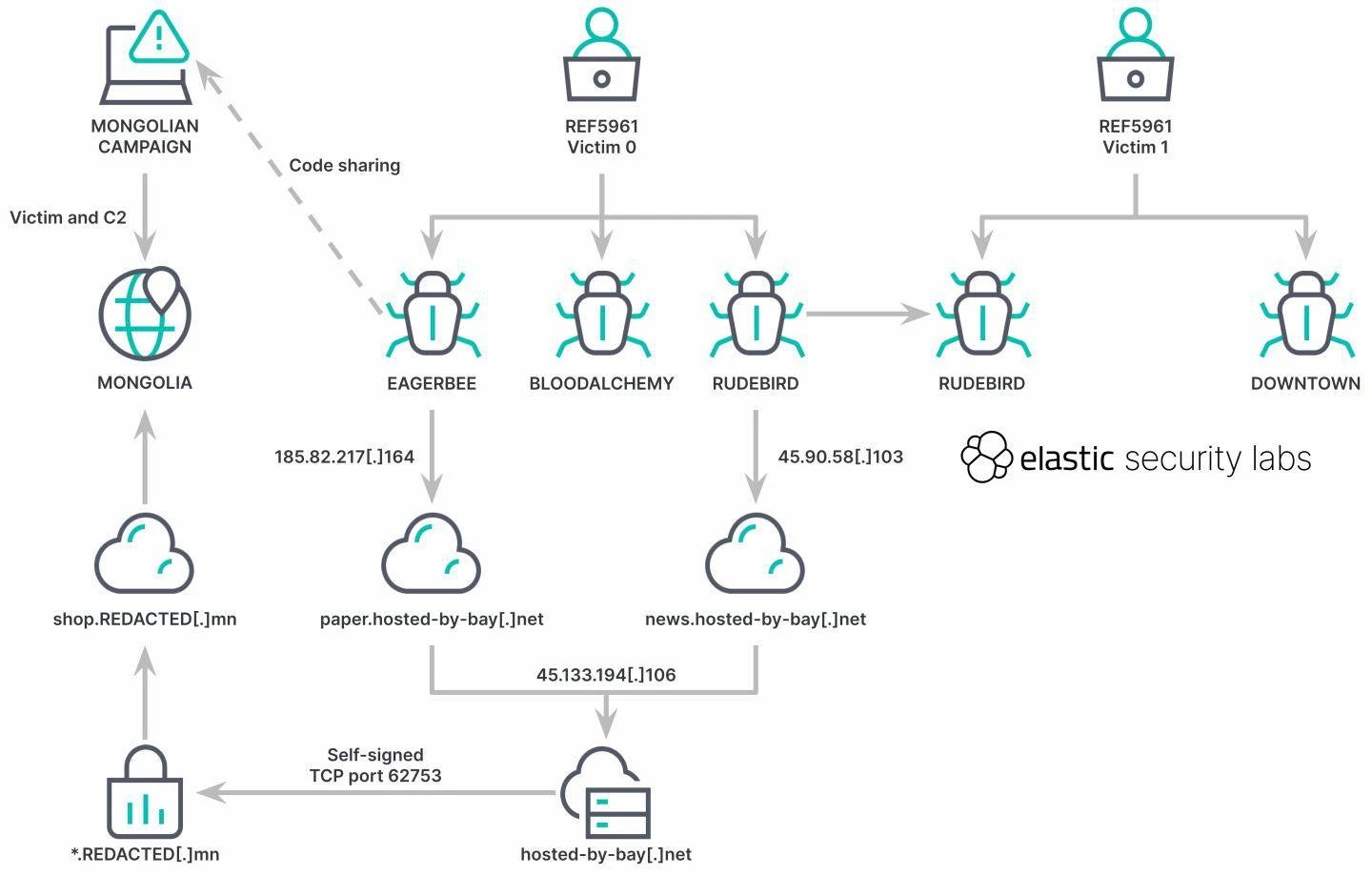
REF5961 intrusion execution flow
[Image Source: https://www.elastic.co/security-labs/introducing-the-ref5961-intrusion-set]
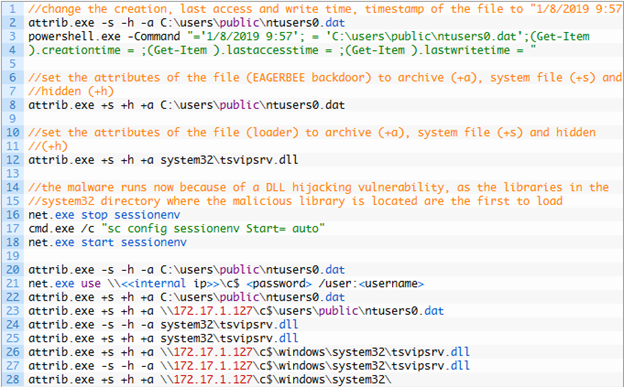
Mechanics of the New Variant:
The new variant features an injector DLL that launches backdoor to collect system data and exfiltrate it to a remote server via a TCP socket. But the exact entry point is still unclear. The server then responds with a Plugin Orchestrator that reports system data and manages running processes. It also injects, unloads, and manages plugins that execute commands for file operations, process management, remote connections, and system services.[5]
The observation team identified the injector named “tsvipsrv.dll” along with the payload file ntusers0.dat, using the SessionEnv service to run the injector, as seen below.
[Image Source: https://securelist.com/eagerbee-backdoor/115175/]
A detailed technical assessment of the variant can be found here: https://securelist.com/eagerbee-backdoor/115175/
Researchers pointed out that “This memory-resident architecture enhances its stealth capabilities, helping it evade detection by traditional endpoint security solutions.”[6]
“EAGERBEE also obscures its command shell activities by injecting malicious code into legitimate processes. These tactics allow the malware to seamlessly integrate with normal system operations, making it significantly more challenging to identify and analyze.”[6]
Building Your Defense:
Safeguarding yourself from an EAGERBEE malware attack requires a combination of proactive measures, cybersecurity best practices, and awareness. Below is a detailed list of suggestions to protect yourself and your systems from this sophisticated threat:
- Regularly update your operating system, browsers, and all installed software.
- Install reputable antivirus and anti-malware programs.
- Do not open emails or attachments from unknown or untrusted sources.
- Only download browser extensions from official browser stores (e.g., Chrome Web Store, Firefox Add-ons).
- Enable features like sandboxing, pop-up blockers, and phishing protection.
- Use strong, unique passwords with multi-factor authentication for all accounts.
- Perform regular backups of important files and store them in a secure, offline location.
- Use network monitoring tools to detect unusual traffic patterns.
- Use the principle of least privilege (PoLP) to limit access to sensitive systems and data.
- Implement Endpoint Detection and Response (EDR) tools on all endpoints like laptops, desktops and servers.
Conclusion:
EAGERBEE malware represents a sophisticated and evolving threat in the cybersecurity landscape, capable of infiltrating systems, stealing sensitive data, and causing significant harm. For the Middle East, where rapid digital transformation and geopolitical complexities intersect, the stakes are even higher. However, by staying vigilant and adopting robust security measures, you can protect yourself and your systems from this dangerous malware. From keeping your software updated and using strong passwords to educating yourself about phishing and deploying advanced security tools, every step you take strengthens your defenses.
Cybersecurity is not a one-time effort but an ongoing process that requires awareness, preparation, and adaptability. By following the best practices outlined in this blog, you can minimize the risk of an EAGERBEE attack and ensure a safer digital experience for yourself and your organization. Stay informed, stay proactive, and prioritize your cybersecurity – it’s your best defense against threats like EAGERBEE.
Reference:
- Cybersecurity Lags in Middle East Business Development: https://www.darkreading.com/vulnerabilities-threats/cybersecurity-lags-middle-east-business-development. Published on December 31, 2024 | Accessed on January 30, 2025.
- EAGERBEE Malware Detection: New Backdoor Variant Targets Internet Service Providers and State Bodies in the Middle East: https://socprime.com/blog/eagerbee-malware-detection. Published on January 08, 2025 | Accessed on January 30, 2025.
- Introducing the REF5961 intrusion set: https://www.elastic.co/security-labs/introducing-the-ref5961-intrusion-set Published on October 03, 2023 | Accessed on January 30, 2025.
- Stealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks: https://thehackernews.com/2024/05/japanese-experts-warn-of-bloodalchemy.html?utm_source=chatgpt.com Published on May 24, 2023 | Accessed on January 30, 2025.
- EAGERBEE, with updated and novel components, targets the Middle East: https://securelist.com/eagerbee-backdoor/115175/ Published on January 06, 2025 | Accessed on January 30, 2025.
- New EAGERBEE Variant Targets ISPs and Governments with Advanced Backdoor Capabilities: https://thehackernews.com/2025/01/new-eagerbee-variant-targets-isps-and.html Published on January 07, 2025 | Accessed on January 30, 2025.


Nice post, Achu! Very informative. Cyber threats are becoming more and more sophisticated, and for Middle East, this poses a serious risk given the region’s geopolitical instability, strategic importance, and reliance on oil and gas industries. Governments and businesses must prioritize cybersecurity by investing in strong defense mechanisms and fostering international collaborations. Critical infrastructure—like power plants, transportation systems, and communication networks—are increasingly vulnerable to disruption or sabotage. A cyberattack targeting a country’s energy supply or national security could have devastating economic and political repercussions, both regionally and globally. Without effective countermeasures in place, these growing threats could have catastrophic consequences, not just for Middle East but for the entire world!
This is a very detailed and well-explained post on the EAGERBEE malware. The link to state-backed groups like REF5961 shows how cyber-attacks are becoming more advanced. The use of hidden techniques like DLL sideloading makes it harder to detect, which is why strong security measures are so important. The tips on keeping software updated and using EDR tools are really useful. Thanks for sharing this great analysis, Achu!
Insightful post, Achu! EAGERBEE malware attacking the Middle East sends a signal into the region, even in modern digital worlds. Its sophistication in service injection and plugin orchestration really shows how cybersecurity threats are moving and changing. This case points to the attribution of malware to a state-sponsored group underlining the geopolitical nature of cybersecurity. A multi-layered approach comprised of robust endpoint protection, regular updating, vulnerability management, zero trust network and security awareness training should be in line to tackle such grave issues. Hence, such emergent challenges put a reward on international cooperation and intelligence sharing to protect digital assets.
Great job, Philip! Your blog does a fantastic job of illustrating how cyber threats are becoming more sophisticated and moving beyond traditional attack vectors. The way EAGERBEE operates using stealthy techniques like memory resident execution and DLL sideloading highlights how advanced persistent threats (APTs) are constantly evolving, often faster than conventional cybersecurity defences can keep up. Your blog serves a strong reminder that staying ahead requires a proactive approach, not just reacting to threats as they arise. Governments, businesses, and cybersecurity enthusiasts like us must constantly adapt to outsmart these ever-changing threats. Keep up the great work!
Great post, Achu!
When it comes to DLL sideloading, the first thing that comes to mind is the widespread practice of downloading cracked software. In an organization with weak cybersecurity measures, a legitimate user who unknowingly installs such software could easily fall victim to DLL sideloading if that was the attacker’s intent.
This highlights the critical need for cybersecurity awareness—it must reach every nook and cranny of the world!
Interesting post!
The EAGERBEE malware shows a serious security vulnerability in the digital systems in the Middle East. The way bad actors continue to evolve their tactics , from DLL sideloading to stealthy backdoors and its ability to infiltrate systems undetected highlights instant need of robust and proactive security strategy. What I found particularly more disturbing is that how malware like this use sophisticated techniques like stealth techniques to bypass the traditional security. This event shows us that cybercriminals are always looking for new ways to take advantage of the system. As cybersecurity professionals its our responsibility to develop advance technology to deal with these bad actors and keep our digital systems safe.
Great Post, Super interesting going into how the EAGERBEE malware uses DLL and malicious code injection into legitimate programs to get control of the affect system and stay undetected. I find it really interesting that this group that is responsible is a Chinese sponsored state actor and that the main targets for theses attacks are ISP’s. I wonder if this is a means to get access and have the capabilities to at any point take theses ISP’s networks down causing these middle east countries to lose internet and communications capabilities. Which would be a huge national security threat for these countries. This also shows that this could happen not only to middle eastern countries but any country in the world. Showing that security should be a top priority for all companies and countries especially for companies responsible for critical infrastructure.
Great article, Achu. Utilizing process injection for privilege escalation is an age-old yet effective method to gain privileged access. However, with the increasing sophistication of cyberattacks, I am concerned that EDR alone may not suffice. It is crucial for organizations to consider implementing XDR for enhanced security.
Great post. This is a crucial reminder that as cyber threats evolve, so must our defense strategies. The emergence of EAGERBEE highlights the importance of proactive security measures, especially in regions undergoing rapid digital transformation like the Middle East. The tactics used by REF5961 highlight how threat actors exploit even well-established infrastructures. Organizations must prioritize threat intelligence, network monitoring, and endpoint security to mitigate risks.
Nice article Achu! EAGERBEE shows how cyber threats are now strategic weapons in global conflicts. With stealth tactics like DLL sideloading, detection is harder than ever. This proves that relying on reactive security isn’t enough—organizations need proactive threat intelligence and adaptive defenses to stay ahead.
What a comprehensive analysis and insightful post overall! This showcases the sophistication and persistence of modern cyber threats. I appreciate how you broke down the operation of REF5961 hacking group and the advanced techniques they employ to remain undetected – like DLL sideloading and obfuscation. I believe it is also crucial to emphasize the importance of training – as always – and regular security audits to identify and mitigate potential vulnerabilities. As cyber threats continue to evolve and become even more sophisticated than before, learning and training will be crucial to a proactive and multi-layered approach so that organizations have at least a fighting chance to stay ahead of the malicious actors.
The post demonstrates exceptional detail and research. The development of EAGERBEE into a stealthy, memory-resident program creates significant security concerns. Detection becomes significantly harder because the malware integrates flawlessly with legitimate system processes. The post offers an excellent dissection of the attack strategies utilized by REF5961. State-sponsored groups demonstrate their advanced persistence through their implementation of DLL sideloading alongside obfuscation techniques. The exploitation of outdated vulnerabilities such as ProxyLogon demonstrates why systems need constant updates and patching to maintain strong defense mechanisms.
Great post, Achu!
When it comes to DLL sideloading, the first thing that comes to mind is the widespread practice of downloading cracked software. In an organization with weak cybersecurity measures, a legitimate user who unknowingly installs such software could easily fall victim to DLL sideloading if that was the attacker’s intent.
This highlights the critical need for cybersecurity awareness—it must reach every nook and cranny of the world!
Very insightful and well-written post, Achu! I learned a lot about how EAGERBEE works and the implications of advanced malware plugins. Of the various safeguarding strategies you had recommended, enabling features like sandboxing, pop-up blockers, and phishing protection stood out to me as this mitigation strategy is simple and can go a long way in protecting our personal and sensitive information. If more individuals took proactive measures such as this, this would help in protecting ourselves from future threats.
Very informative post, Achu. The evolution of malware cyber-attacks has been marked by increasingly sophisticated obfuscation techniques. As noted by Hammi et al. (2024), “The challenge of detecting malware remains an ongoing issue, as malware authors continuously develop new techniques to evade traditional signature-based detection methods” [1]. Despite this, Endpoint Detection and Response (EDR) solutions continue to rely on conventional malware signature databases, which may be insufficient in identifying advanced threats. To enhance the malware cybersecurity defenses, it is essential to adopt a multi-layered Threat Intelligence framework that integrates existing cyber solutions to collaboratively detect sophisticated malware attacks. Keim et al. (2022) proposed a Cyber Threat Intelligence framework that retains the advantages of traditional models while significantly improving the detection of all major malware types [2].
[1] Hammi, B., Hachem, J., Rachini, A., Khatoun, R., & Aissaoui, H. (2024). Malware Detection Through Windows System Call Analysis. Proceedings of the … Conference on Mobile and Secure Services (MOBISECSERV) (Online), CFP24RAC-ART, 1–7.
[2] Keim, Y., & Mohapatra, A. K. (2022). Cyber threat intelligence framework using advanced malware forensics. International Journal of Information Technology (Singapore. Online), 14(1), 521–530.
The article covers EAGERBEE malware, its evolution, and how the REF5961 group exploits vulnerabilities to infiltrate systems. It highlights stealth tactics like DLL sideloading and memory-resident execution, making detection harder. The piece also provides mitigation strategies to protect against such threats.